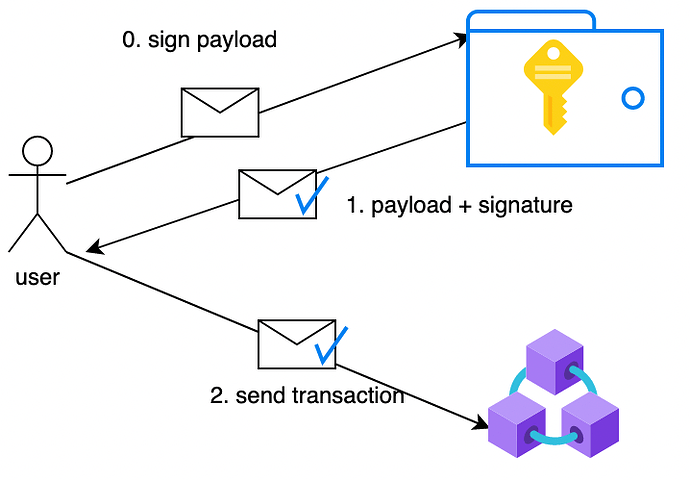
Classic signing with a wallet
As a quick remember, here is the common flow :
-
The user sends a request to his wallet to sign a payload
-
The wallet signs the payload with the private key and returns the signature
-
The user forwards the signed message to a Tezos node
- The wallet can be local or distant.
- If remote, there is a risk over the communication channel and third parties
- Each wallet will use its own mechanism to protect the private key: password, etc …
Biometrics signing
Biometrics on Android provides a convenient method for authorizing access to private content within your app. Instead of having to remember an account username and password every time they open your app, users can use their biometric credentials to confirm their presence and authorize access to the private content
Your phone, depending on the security level of the chip, becomes your HSM (Hardware Secure Module) replacing external devices like a Ledger or a Yubikey.
There are two approaches on Tezos to use Biometrics :
Solution 1: Use your phone Biometrics to protect the private key
This solution is similar to the signing with a wallet solution
Details :
- the wallet is the secure chip of the phone, it is a local communication
- the private key is protected by the phone Biometrics
Initialization
Biometrics just controls the access to the keypair.The keys are generated from a native Android algorithm, a crypto library as spongycastle or just an encrypted private key as string.Once the user has authenticated with Biometrics, he has access to the protected object on the Keystore.
If you want to learn more about this announcement, please read our blog post on Marigold website ![]()
Signing on Tezos with Android Biometrics

.drawio(1).svg)